How Does Zcash Enable Private Transactions? A Detailed Guide to zk-SNARKs
Blockchain systems typically rely on public ledgers for decentralized verification. However, this transparency also exposes transaction data to all participants. In scenarios involving financial security or sensitive information, fully transparent transaction records can lead to privacy leaks and data analysis risks.
Against this backdrop, zero-knowledge proof technology has emerged as a key direction for blockchain privacy. By introducing zk-SNARKs, Zcash applies cryptographic proofs to the transaction verification process, making it possible to achieve both privacy and verifiability at the same time. This represents a leading example of combining privacy-preserving computation with blockchain technology.
The Role of zk-SNARKs: The Core of Zcash Privacy
zk-SNARKs are the foundational technology behind Zcash’s private transactions. The term stands for “Zero-Knowledge Succinct Non-Interactive Argument of Knowledge.” It allows one party to prove that a statement is true without revealing any additional information.
In Zcash, zk-SNARKs are used to prove that a transaction satisfies a set of constraints, such as valid fund sources, balanced inputs and outputs, and the absence of double spending. This allows the network to verify transactions without exposing their details, enabling privacy.
The Logic of Zero-Knowledge Proofs: Proving Without Revealing
Traditional verification methods depend on data disclosure, such as revealing transaction amounts or account balances. Zero-knowledge proofs take a different approach. They construct mathematical proofs that allow a verifier to confirm that certain conditions hold true without accessing the underlying data.
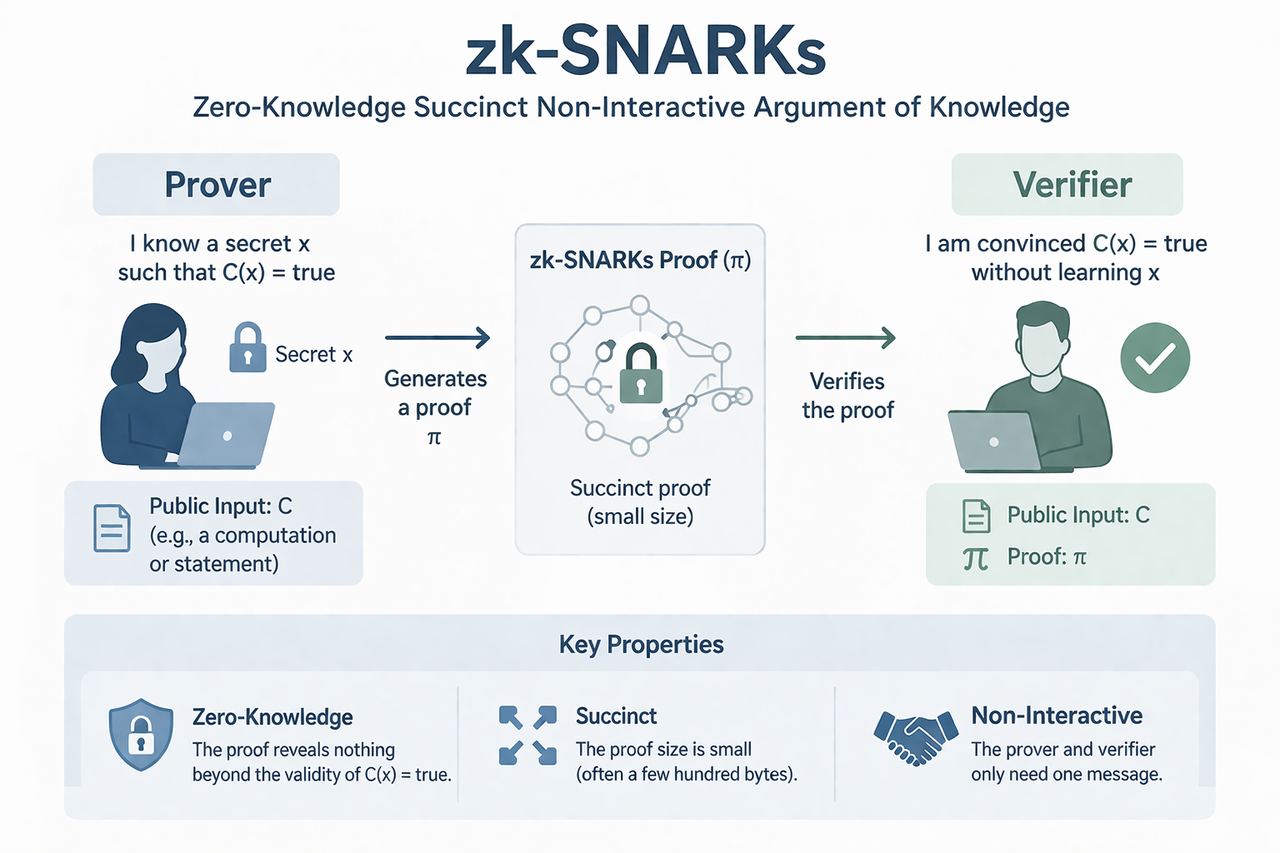
This process relies on three core properties. First is completeness, meaning valid statements can be successfully proven. Second is soundness, ensuring false statements cannot pass verification. Third is zero-knowledge, meaning the proof reveals no additional information beyond the validity of the statement.
Through this mechanism, Zcash can verify transactions without exposing their contents, enabling true privacy.
Key Features of zk-SNARKs
zk-SNARKs have several defining properties that make them suitable for blockchain systems.
“Succinctness” means the generated proofs are small and efficient to transmit. “Non-interactivity” allows verification to be completed without multiple rounds of communication. “Argument of knowledge” ensures that the prover genuinely possesses the required information rather than fabricating it.
Together, these features allow zk-SNARKs to deliver strong privacy guarantees while still meeting the efficiency and security requirements of blockchain networks.
How zk-SNARKs Work Within Zcash
In Zcash private transactions, zk-SNARKs operate alongside several supporting data structures.
“Commitments” are used to encrypt and store transaction amounts and address information. “Nullifiers” mark funds as spent, preventing double spending. Additionally, the “shielded pool” holds all private assets, making it difficult to link transactions directly.
These structures work together to create a system that hides data while maintaining consistency and integrity.
The zk-SNARKs Proof Generation Process
When a user initiates a private transaction, they must generate a zk-SNARK proof to demonstrate its validity.
This process begins by converting transaction logic into mathematical expressions, often represented as arithmetic circuits that describe how funds move. These expressions are then transformed into specific mathematical problems, and a proof is generated using private input data.
Because this involves complex computation, proof generation is resource-intensive. This is one of the defining performance characteristics of private transactions.
Verification: How the Network Confirms Validity
Compared to proof generation, zk-SNARK verification is highly efficient.
Once a transaction is broadcast to the network, nodes only need to verify the attached proof to confirm that all rules are satisfied. They do not need access to any underlying data. This approach preserves privacy while reducing the computational burden on the network.
As a result, Zcash can achieve secure validation similar to traditional blockchains, without revealing transaction details.
Trusted Setup: A Critical Requirement
zk-SNARKs rely on an initial parameter generation process known as a “Trusted Setup.”
During this process, a set of public parameters is created for use in proof generation and verification. If compromised, it could affect the system’s security. To mitigate this risk, Zcash employs techniques such as multi-party computation (MPC) to reduce trust assumptions.
As technology evolves, newer approaches that eliminate the need for trusted setup are being explored to further enhance security and decentralization.
Advantages and Limitations of zk-SNARKs
The main advantage of zk-SNARKs is their ability to provide strong privacy while maintaining efficient verification. This makes them a major direction in blockchain privacy technology.
However, there are also clear limitations. Proof generation is computationally intensive and resource-demanding. Early implementations rely on trusted setup, which has been a point of concern. Additionally, technology is complex, raising the barrier for development and adoption.
Comparing zk-SNARKs with Other Privacy Technologies (Monero as an Example)
Unlike Zcash, which uses zk-SNARKs, Monero relies on ring signatures and obfuscation techniques to achieve privacy.
zk-SNARKs provide “complete hiding” through mathematical proofs, while ring signatures achieve “probabilistic anonymity” by mixing transactions among multiple participants. These approaches differ significantly in privacy strength, performance, and implementation.
This contrast reflects two distinct design philosophies in privacy-focused cryptocurrencies: one prioritizes precision and verifiability, while the other emphasizes default anonymity and obfuscation.
Conclusion
zk-SNARKs are the core mechanism behind Zcash’s private transactions. By using zero-knowledge proofs, they enable transaction verification without revealing any data. This technology successfully combines privacy with verifiability in blockchain systems, offering a viable path for privacy-preserving computation.
As zero-knowledge proof technology continues to evolve, its applications are expanding beyond privacy coins into broader areas of blockchain and data systems.
FAQs
What is the difference between zk-SNARKs and traditional encryption?
Traditional encryption hides data, while zk-SNARKs prove that certain conditions are true without revealing the data itself.
Why can zk-SNARKs hide transaction details?
Because verification relies on mathematical proofs rather than the original data.
Are zk-SNARKs completely secure?
Their security depends on cryptographic assumptions and implementation. They are currently considered reliable but continue to evolve.
Why is generating zk proofs resource-intensive?
Because it involves converting complex logic into mathematical proofs and performing heavy computations.
Do all Zcash transactions use zk-SNARKs?
No, only transactions involving shielded addresses (z-addresses) use this technology.
What is the difference between zk-SNARKs and zk-STARKs?
zk-STARKs do not require a trusted setup but typically produce larger proofs. The two differ in design goals and implementation approaches.
Related Articles

In-depth Explanation of Yala: Building a Modular DeFi Yield Aggregator with $YU Stablecoin as a Medium

Sui: How are users leveraging its speed, security, & scalability?
AI-Native Settlement Layers: How United Stables Is Building the Next Financial Rail
The ve(3,3) Flywheel Explained: How AERO Tokenomics Powers Aerodrome’s DeFi Economy
How Does PAXG Work? In-Depth Overview of the Physical Gold Tokenization Mechanism