Zhang Wen's laptop hard drive cracking stuck: What is BitLocker encryption? Why does it take until the universe's destruction to crack?
North Taipei Metro Random Killings Case Suspect Zhang Wen’s Laptop Hard Drive Protected by BitLocker Encryption, Police and Forensics Hit a Roadblock. What Is BitLocker Encryption Technology? Why Is It Difficult to Crack Even with Supercomputers in a Short Time?
North Taipei Metro Random Killings Case Follow-up: Zhang Wen’s Laptop Hard Drive Stuck in Cracking
According to United News Network, the suspect Zhang Wen, who committed the random attacks in the Zhongshan South West commercial district, had his portable tablet unlocked by Taipei City Criminal Investigation Brigade. However, the key evidence may be hidden in a laptop at his rental residence.
After the crime, Zhang Wen committed suicide out of guilt. Although the laptop was deliberately burned, fortunately, the internal SSD solid-state drive was not severely damaged and remains operational.
However, the hard drive is protected by Microsoft’s BitLocker encryption, making data inaccessible through ordinary means. Currently, investigators have issued a formal request to the original manufacturer Asus and software provider Microsoft for technical assistance, while also attempting to restore the data via brute-force cracking methods.
Nevertheless, regarding the success of unlocking the hard drive, police admit they are not very confident and it largely depends on the security level set by the suspect.
What Is BitLocker Encryption Technology?
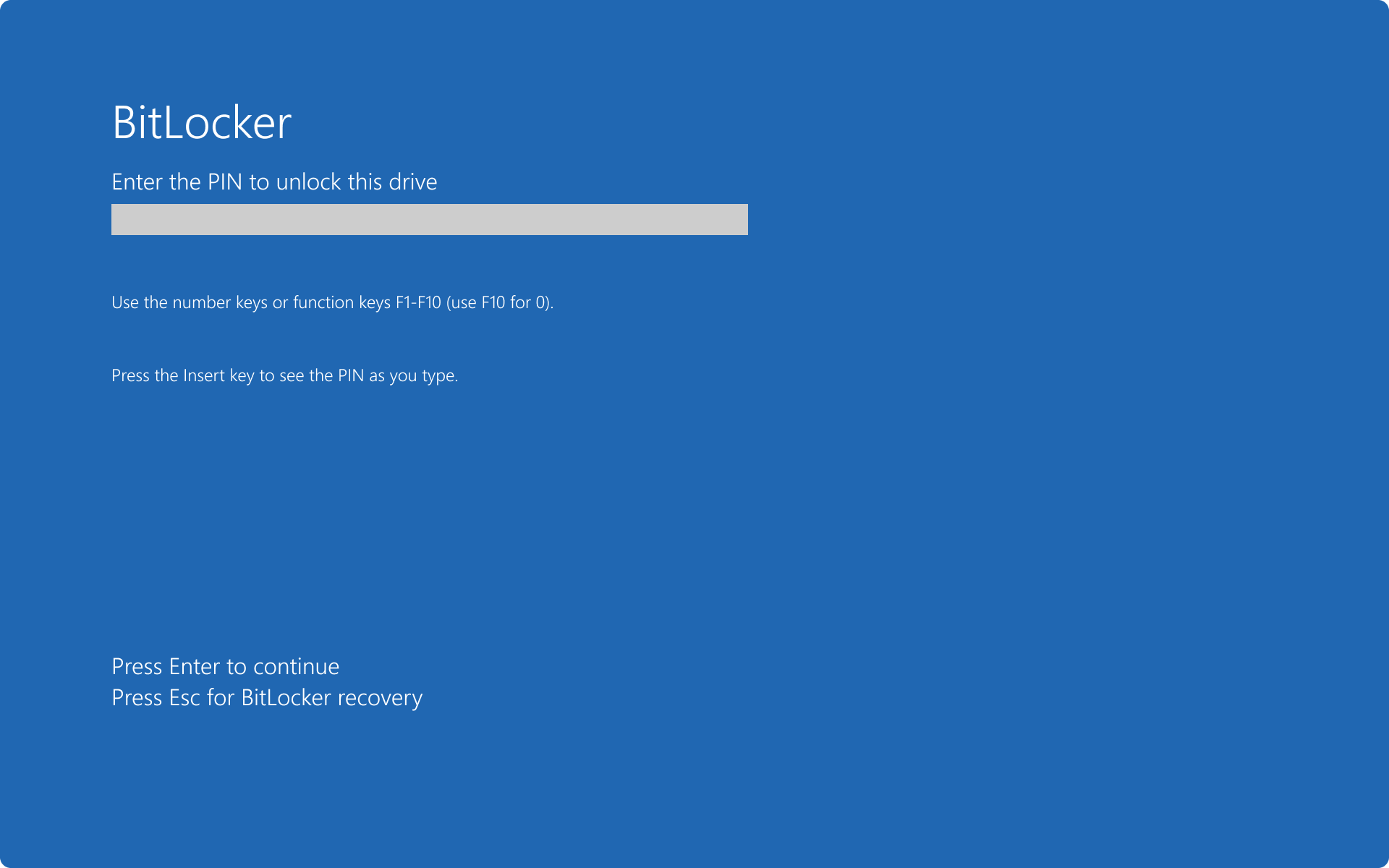
According to Microsoft’s official description, BitLocker is a built-in data protection feature in Windows operating systems, designed specifically to prevent data theft or leakage.
Its working principle is to encrypt the entire disk drive, operating in conjunction with the Trusted Platform Module (TPM) embedded in the hardware.
Image source: Microsoft BitLocker is a built-in data protection feature in Windows operating systems, designed specifically to prevent data theft or leakage.
When BitLocker detects that the hard drive has been moved to another device or attempts to read data offline, the system will automatically lock and require the user to input a 48-digit “recovery key”.
This design was originally intended to protect user confidential information if the computer is lost or stolen, ensuring that even if the hardware is taken, the internal files cannot be accessed by unauthorized persons.
Can BitLocker Be Recovered?
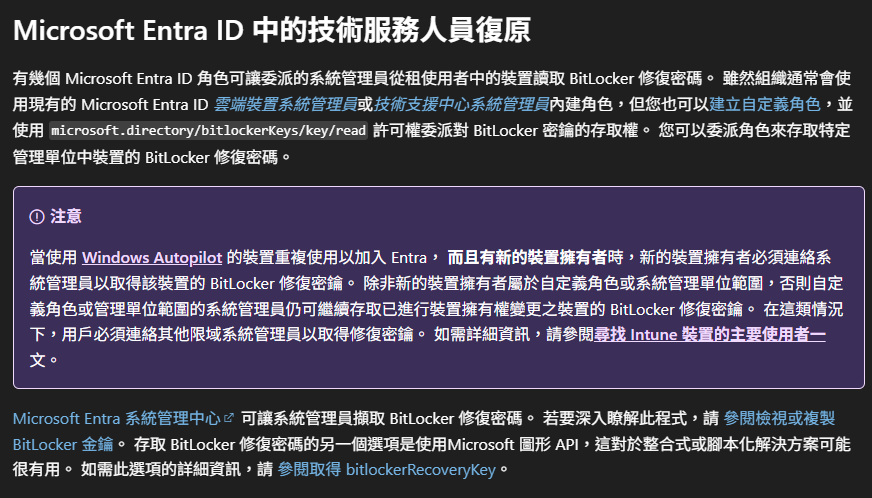
Besides entering a user-set password, Microsoft also lists several legitimate methods for BitLocker recovery and unlocking, but these largely depend on the user’s prior backup habits or enterprise environment settings:
- Microsoft Entra ID Self-Recovery: If the user has backed up the key to the cloud, they can log into their Microsoft Entra ID account page and view the BitLocker key under device options.
- USB Drive Recovery: If the user has stored the recovery password as a text file on a USB flash drive, inserting the device into the locked computer will allow unlocking following the instructions.
- Enterprise Technician Assistance: In corporate or organizational domain environments, administrators can retrieve recovery information via Active Directory or use Data Recovery Agent (DRA) to mount the encrypted drive on another machine for unlocking.
Image source: Microsoft Besides entering a user-set password, Microsoft also lists several legitimate methods for BitLocker recovery and unlocking
This also means that unless the police can access Zhang Wen’s Microsoft cloud account, find the USB containing the key, or the laptop belongs to a corporate domain (which is highly unlikely), without that 48-digit recovery key, the hard drive is like a welded digital safe—difficult to open.
Zhang Wen’s Laptop Cracking Is Very Difficult, Lawyer: Only Until the Universe’s End Can It Be Cracked
However, brute-force cracking the 48-digit recovery key in a short period is nearly impossible.
Security lawyer Xu Shiwei, who previously served as a prosecutor, analyzed that the BitLocker recovery key consists of 48 decimal digits, and its combination complexity is slightly greater than 2^159. After subtracting checksum and structural restrictions, its strength is still equivalent to 2^128.
Even with the world’s fastest supercomputers today, performing 1.8×10^19 operations per second, trying all possible password combinations would take nearly 6 billion years. He described it as only possible to crack when the universe is destroyed.
Even if future quantum computing technology matures and significantly increases computational speed, Xu Shiwei estimates that the decryption time could be reduced to the square root level, but still would take about 32 million years.
As for why the Criminal Investigation Bureau still decided to attempt cracking, Xu Shiwei speculates that the reasons may include, police hope that manufacturers have an undisclosed backdoor, attempting to unlock through unofficial channels; or due to social pressure and higher-ups’ demand for solving the case, so even knowing the chances are slim, the police must demonstrate their determination to exhaust all possible means.