IOSG: The Future Beyond Privacy of TEE
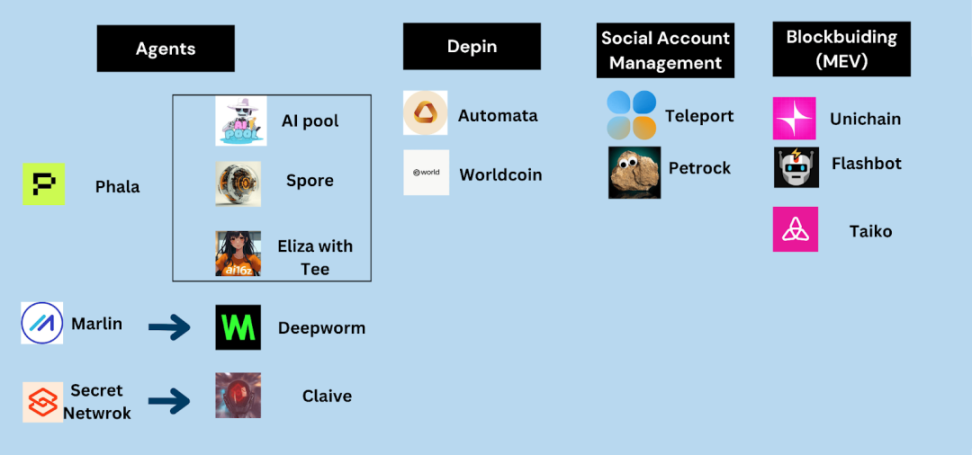
The TEE hardware in the Decentralization network creates a trusted computing environment, known as Decentralized Confidential Computing, which has spawned many interesting and market-focused use cases in the encryption field, including Agent, DePIN, and social media account management.
Author: Yiping, Jiawei, Danny, IOSG
What is TEE?
TEE isolates sensitive data in a protected CPU isolation zone during processing. The content of the isolation zone (including the data being processed and the processing methods) is only visible to authorized program code, and cannot be accessed or understood by anyone or anything else (including cloud service providers).
▲ Source: Twitter
The configuration of TEE determines which entities are authorized to input data, the data sets and program types that can be processed, and the allowed output results. One of the core functions of TEE is to verify its correct configuration through a separate authentication process. The authentication process provides encryption verification for the hardware and configuration elements of TEE, ensuring the security of its isolated processing.
The development and evolution of TEE
The evolution of TEE mainly revolves around three concepts:
- Developer Experience
- Performance
- Security
Developer Experience
Intel SGX has revolutionized secure hardware, providing strong isolation capabilities close to native performance, but its developer experience faces challenges. Developers need to extensively rewrite their applications to adapt to SGX’s programming model, and this complexity limits its applications to a few areas such as key management.
With the introduction of frameworks like Gramine, the developer experience has been significantly improved. Gramine provides software abstraction for CPU isolation zones, allowing developers to directly compile applications into binary files and run them in SGX. Gramine acts as a “glue” that connects the SGX environment with the regular Linux environment.
Performance Improvement
With the development of TEE into Confidential VMs and GPUs (such as Intel TDX and H200), developers can deploy unmodified applications directly. Developers can package the entire production environment and run it directly on the encryption virtual machine. H200 is the first product to offer GPU-level TEE, capable of running more AI and image processing-related applications.
For example, the dStack platform further simplifies the deployment and scaling of developers in a confidential computing environment. Based on a microservices architecture, dStack supports the deployment and secure communication of multiple microservices in a single TEE instance. This modular design allows more complex workflows to run securely in the TEE.
Security
The security of TEE depends on the trust root provided by the hardware manufacturer, but this also brings concerns about the reliance on proprietary hardware and closed-source implementations, which may lead to transparency and potential backdoor concerns. To address these issues, open-source TEE solutions (such as Keystone and OpenTEE) are gradually becoming viable alternatives. Although the current performance lags behind proprietary solutions, their transparent design and verifiable manufacturing process enhance the trust in hardware integrity.
Developers can also combine multiple TEEs from different vendors to run the same workloads and compare the output results, thus reducing the risk of potential vulnerabilities in a single TEE through this cross-validation.
Another key security challenge is side-channel attacks. These attacks extract sensitive data from TEE through physical characteristics such as time, power consumption, or electromagnetic leakage. A novel solution is to deploy TEE in a completely isolated environment. For example, the SpaceCoin project plans to launch TEE into orbiting satellites to eliminate proximity-based attack threats through the physical isolation of the satellite. By running computations in space, these TEEs provide protection against side-channel attacks and other physical threats.
The Future of TEE
As TEE further develops, the trade-offs become more complex:
- Improving the developer experience may increase the Trusted Computing Base (TCB).
- Open source instruction sets may reduce performance, but increase verifiability.
- Improving the TCB through the Yocto project may make the deployment more complex.
From creating engaging social experiences, to building a fair global financial system, training large models with sensitive data, and achieving global-scale privacy identity management, we need to reach the fifth level of TEE - the holy grail of encryption computing, and the future prospects are exciting.
Early TEEs (such as SGX) required developers to write custom C code or use abstraction layers like Gramine to provide Linux-like interfaces.
Advanced solutions (such as TDX and Nitro) now support containerized workflows similar to Docker, but debugging remains difficult.
Paradigm envisions multi-isolation zone collaboration using multiparty computation (MPC) or fully homomorphic encryption (FHE) to mitigate the risk of single isolation zone failure.
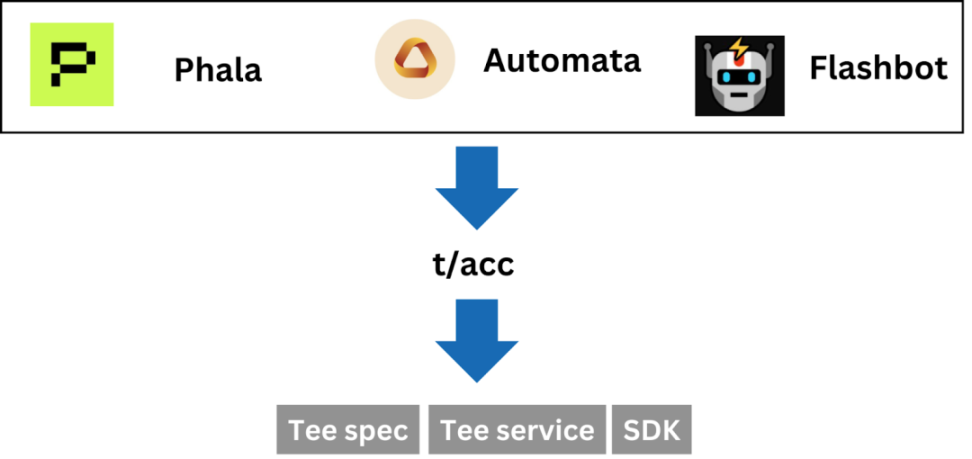
For Crypto x TEE, Phala, Automata, and Flashbot are driving the establishment of standards. By providing standards and improving Tee-related infrastructure services, Crypto TEE can be quickly adopted by more protocols.
▲ Source: IOSG
Use Cases of TEE
The TEE hardware in the Decentralization network creates a trusted computing environment, known as Decentralized Confidential Computing, which has spawned many interesting and market-focused use cases in the encryption field, including Agent, DePIN, and social media account management. Among many emerging infrastructures, Unichain, Flashbots, and Taiko are also leveraging TEE to optimize their services.
▲ Source: IOSG
MEV Related Use Cases
As a pioneer in the MEV field, Flashbots began exploring the role of privacy technologies like TEE in the transaction lifecycle as early as December 2022. Its main goal is to achieve trust-minimized collaboration in the transaction supply chain, including Decentralization block construction and order flow sharing. Flashbots has conducted a series of research and experiments related to TEE, such as running the Ethereum client Geth in Intel SGX and executing block builder operations in SGX.
For a long time, 90% of Ethereum blocks were built by just two block builders, posing a constant risk to Ethereum’s Decentralization, resiliency, and censorship resistance. To enhance the Decentralization of block building, Flashbots has launched BuilderNet, an Ethereum Decentralization block building network powered by TEE. The network also supports providing refunds to upstream order flows from dApps, wallets, and users, while ensuring security and performance.
Subsequently, Flashbots ceased the operation of its centralized block builder on the mainnet and migrated to BuilderNet. Currently, Ethereum’s top-ranked block builder, Beaverbuild, has also integrated its software, infrastructure, and order flow into this Decentralization network.
A few months ago, Flashbots, in collaboration with Uniswap Labs and OP Labs, launched Rollup-Boost on Unichain, which is a TEE-supported verifiable Rollup block construction platform.
Based on similar TEE coprocessor technology, Flashbots has also released Teleport - an application that uses TEE coprocessors to enable smart contracts to control Twitter accounts.
AI-related use cases
The combination of Crypto and AI has given birth to many links, as explained in IOSG’s previous articles. With the increasing support for TEE running on GPUs, the demand for TEE in various links of AI has been realized, including (.
- Data Collection & Annotation
- Model Training
- Model inference
- Autonomous agent
Data Collection & Annotation
Under the influence of Scailing law, data has become the most important part of AI development. Crypto can provide the greatest help to AI in the data layer through the mechanism of Decentralization, encouraging users to contribute private data and data annotations to make up for the lack of access to datasets, especially annotated data, in public networks. TEE can improve the privacy and security of data collection and annotation.
In the case of Vana, for example, Vana is a Decentralization data network where Satya-type validators specialize in providing TEE environments. Through TEE validators, the Data Liquidity Pool (DLP) in Vana, which acts as a data marketplace, is able to ensure the traceability and accuracy of data and provide data securely without exposing the original data. The user submits the encryption data to the smart contract, and the smart contract creates an asset identity for the user. User data is transmitted to the TEE node via an end-to-end encryption protocol (such as TLS), where the data is decrypted to generate a proof of quality.
From the user’s perspective, TEE transforms data into verifiable assets, turning data into a form of “usage rights”. Users retain ownership of their data, receive corresponding token rewards, and participate in decision-making through governance mechanisms.
![])https://img.gateio.im/social/moments-1ac587ce93afd6ec77765f47dd2bf3aa(
▲ Source: Phala 2025 Report
Especially for sensitive data such as medical or financial, TEEs make the provision and labeling of data private. This is critical to maintaining user confidence, bold data, and compliance with data protection regulations such as GDPR and CCPA.
Model Training
The independence of TEE means that it is the best place for model training. With the popularization of GPU-based TEE and the improvement of hardware performance, TEE can support more training scenarios. Currently, through Nvidia H200 GPU, fine-tuning can be performed on open-source models such as Llama-3.1-8B, which not only ensures the isolation and encryption of training data and computation, but also generates encryption proof and model fingerprints for public verification. Under appropriate parameters, the model training performance of TEE is sufficient to support most models. Training Llama-3.1-8B in TEE with H200 GPU, 30 rounds of training can be completed in just 1 hour, achieving an accuracy rate of 98%, with almost no performance loss.
The nature of Tee dependency on hardware determines the need for a Decentralization GPU network to support its training stability. For example, Hyperbolic utilizes TEE to support AI training between distributed nodes, with lower costs compared to centralized GPU providers like OpenAI, while also providing verifiable execution proofs.
![])https://img.gateio.im/social/moments-462fd907769f11c7e9880808e72156b4(
▲ Source: Phala 2025 Report
Platforms with strong demand for AI training can easily access TEE technology, such as Near, which collaborates with Phala to build TEE model training capabilities.
![])https://img.gateio.im/social/moments-abe4fccf99f2c84e20e0df3b420f7b48(
▲ Source: Twitter
Model Inference
From the user’s perspective, the most important thing is whether the use of the model has actually undergone the corresponding model calculation. From the Chatgpt interface to the open-source models within the TEE environment. The inference process supported by TEE can verify the inference results of the model. Nvidia GPU TEE allows the inference process to protect user privacy without sacrificing speed and accuracy. Services like Phala’s confidential AI inference generate verification proofs for each output, allowing users to verify whether the inference truly occurs within the TEE, enhancing trust in AI output results. Platforms like 0G integrate TEE into AI inference services, ensuring end-to-end data protection and verifiability from request to response.
![])https://img.gateio.im/social/moments-40fc5059e59bdf02f38802ebe5ea026e(
▲ Source: Phala 2025 Report
Platforms with strong demand for AI training can easily access TEE technology, such as Near, which builds TEE model training capabilities together with Phala.
![])https://img.foresightnews.pro/202501/37f6d690e9ca8ec34061223771a74658.png?x-oss-process=style/scale70(
▲ Source: Twitter
Autonomous agent
Crypto Agent is gradually becoming an important participant in on-chain activities. To enable agents to participate more effectively in the on-chain financial system, they need to be given autonomy and sovereignty.
Autonomy means that the operation, decision-making, input, and output of the agent are not subject to human interference. For example, autonomy means that the inputs and outputs pushed by Truth Terminal cannot be controlled by Andy. At present, although it is not direct intervention, there is still a suspicion of background prompt guidance. Sovereignty, on the other hand, emphasizes ownership. This includes Crypto assets and computing resources. Agents have 100% control over assets and independent control over their operating environment.
The autonomy and sovereignty of the agent are prerequisites for enabling more use cases. Only agents with autonomy can play roles in more economic activities. At the same time, this is an unprecedented social experiment that can only occur in Crypto, and any progress is a super Meme that will generate significant attention economy in the crypto market.
Currently, the most widely used ai16z Eliza framework has integrated TEE technology, and developers can quickly deploy agents with TEE features through Eliza. Agents can autonomously gain control over Twitter accounts, wallets, and computing resources through TEE.
The earliest TEE agent experiment came from Pet rock, an agent that runs in the TEE environment and has control over Twitter permissions. The later AI pool leverages the characteristic of operation in the TEE without external interference, providing a fair and random launchpad. Just send money to a specific address, and the agent will be initialized with secure parameters. After initialization, when the money sending process is completed, the agent will automatically select a random time, random ticker, and deploy liquidity and launch tokens. All of these operations run in a TEE-protected environment, which is beyond human interference. Spore.fun showcases the process of wallet management by agents through TEE.
Any TEE agent has a corresponding verification process that allows users to verify whether the agent is running in TEE at any time and whether the related permissions are truly beyond human control. This can also be achieved through ZK in addition to TEE.
Many TEE projects are trying to collaborate with Agent projects to create some innovative gameplay.
![])https://img.gateio.im/social/moments-96de8401a7ce943ee436ee9c44bfa083
▲ Source: IOSG
As Agent becomes more intelligent, its role in the on-chain ecosystem becomes more important, and the importance of reducing its dependence on human influence is higher. Embedding TEE in the agent’s lifecycle is the most visible implementation approach.
Conclusion
For Crypto, TEE is currently a trusted computing tool with strong availability and fast application development. Its development revolves around three directions: developer experience, performance, and security, and is also limited by hardware. With the development of GPU dominated by NVIDIA, TEE gradually transitions from SGX to TDX.
On the application level, AI, social, and DEP are the strong directions of Toc, while blockchain construction is the infrastructural application direction. With the development of AI narrative, TEE can contribute to the computation privacy, model/data traceability capability of different AI links on decentralization computing, and endow the Agent with the ability to run independently and autonomously. Social and DEP are new retail directions that are constantly being explored. For the operation of the blockchain itself, TEE will play an important role in node capabilities in the future, bringing privacy and fairness to the blockchain.
As the underlying services/SDKs become more mature, the threshold for various projects to use TEE technology is also getting lower. Service providers focusing on TEE for crypto applications are accumulating towards standardized and unified open source technology support, and have already given birth to many new use cases. With such vertical integration, we expect to see more explosive growth in TEE-based applications.