Bing AI search results poisoned, malicious OpenClaw installer stealing confidential information

SlowMist Chief Information Security Officer 23pds posted on the X platform on March 10th warning that attackers have carried out “poisoning” attacks on Bing AI search results, pushing fake OpenClaw installers to the top of search results for “OpenClaw Windows,” tricking users into downloading and executing malicious programs.
Attack Method: How Malicious Repositories on GitHub Pollute Bing AI Search
(Source: Huntress)
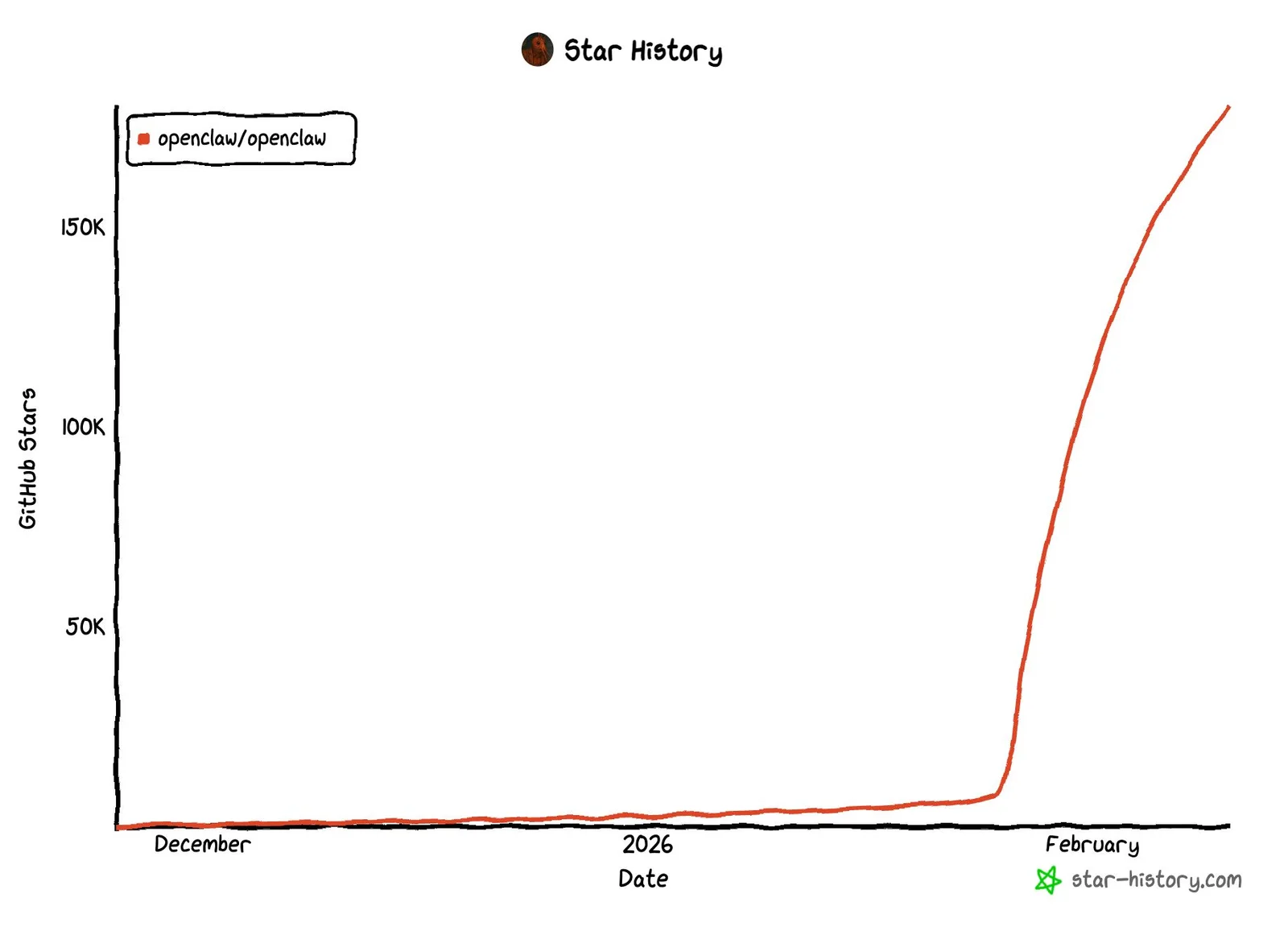
OpenClaw is a rapidly growing open-source AI assistant tool with a large user base, originally named Clawdbot (launched November 2025), which quickly gained tens of thousands of forks and hundreds of thousands of stars on GitHub. Its popularity has become an entry point for attackers.
Attackers created malicious repositories on GitHub disguised as legitimate installers, using legitimate code from Cloudflare to increase credibility, and published under the independent GitHub organization name “openclaw-installer,” rather than a regular user account, further avoiding initial suspicion.
Huntress points out that the success of this attack hinges on: simply hosting malicious code on GitHub is enough to pollute Bing AI search recommendations, without any additional manipulation of search engine algorithms. This method is a continuation of the December 2025 attack where attackers exploited ChatGPT and Grok shared chat features, but with lower barriers and broader impact.
Malicious Toolkit Analysis: Three-Layer Malicious Software Threat
The malicious components deployed in this attack are clearly divided:
Stealth Packer (New Type of Packager): Injects malicious code into memory, adds firewall rules, creates hidden ghost scheduled tasks, and performs anti-virtual machine checks (detects mouse movement to determine if in a real environment). Detected very rarely on VirusTotal.
GhostSocks (Reverse Proxy Malware): Previously used by the BlackBasta ransomware group, turns infected computers into proxy servers, allowing attackers to log in with the victim’s IP address, bypassing multi-factor authentication (MFA) and anti-fraud detection mechanisms.
Information Stealer (Vidar / PureLogs Stealer): Written in Rust, runs as a loader in memory, stealing credentials, API keys, and OpenClaw configuration files; variants of Vidar even use Telegram channels and Steam user pages to hide dynamic C2 command addresses.
Cross-Platform Infection: Different Invasion Paths for Windows and macOS
Malicious GitHub repositories provide installation instructions for both platforms. On Windows, executing “OpenClaw_x64.exe” deploys multiple Rust-based malicious loaders, with information stealers quietly running in memory. On macOS, the installation guide requires running a one-line bash command to pull “OpenClawBot” from another malicious organization’s “dmg” repository, confirmed as a variant of AMOS, which disguises itself as an administrator permission request to steal sensitive data from folders like Documents, Downloads, and Desktop.
After Huntress discovered and reported the malicious repositories to GitHub, they were closed within about 8 hours. Notably, even legitimate versions of OpenClaw contain configuration files with highly sensitive information (passwords, API keys, etc.). If the system has been compromised by the info-stealing malware, these files are also at risk of theft.
Frequently Asked Questions
Q: Why are malicious programs recommended in Bing AI search results?
Attackers found that hosting malicious code on GitHub is enough for Bing AI’s recommendation system to push malicious repositories to the top. The AI system’s evaluation of GitHub repository trustworthiness fails to effectively identify malicious content, allowing attackers to exploit the platform’s inherent trust to deceive.
Q: How does GhostSocks malware bypass multi-factor authentication?
GhostSocks turns the infected computer into a proxy server, enabling attackers to log into compromised accounts using the victim’s IP address. Since login behavior appears consistent with the victim’s usual location and network environment, MFA and anti-fraud mechanisms have difficulty detecting these as abnormal accesses.
Q: How to identify fake OpenClaw installers?
Legitimate OpenClaw should be downloaded directly from the official GitHub repository. For macOS installation, if prompted to run a bash one-liner from an unknown organization’s repository, it should be considered highly dangerous. Users should not blindly trust code repositories on GitHub—hosting on a trusted platform does not guarantee the software’s safety.
Related Articles
French Authorities Boost Security for Crypto Executives Amid Kidnapping Threats
Zonda Exchange Discloses 4,500 BTC Cold Wallet as Private Keys Remain Untransferred
The OneCoin Ponzi scheme begins restitution, with the U.S. Department of Justice setting aside $40 million to compensate victims
Ukraine Dismantles International Cybercrime Ring, Seizes $3M in Cryptocurrency
DeFi Sector Faces Multiple Pressures as Yields Fall and $285M Hack Raises Security Concerns